Operational Risks
March 5, 2021
Risk Management | RiskWatch Blog
What is Operational Risk?
Operational risk, as defined by the Risk Management Association, is the risk of loss resulting from inadequate or failed internal processes, people, and systems, or from external events, but is better viewed as the risk arising from the execution of an institution’s business functions.
To simplify that, you could just say it’s the inherent risk of running a business. It is the possibility that something could go wrong, affecting your company’s operations.
Top Operational Risks
There are a lot of operational risks. Of course, “a lot” is referring to pretty much any risk that exists in your business. Since that would be quite along read, for the sake of this blog we will limit this to the five top operational risks. These aren’t necessarily the risks that will cause the biggest impact to your organization, but are applicable to many companies and are ones you should recognize.-
IT Disruption
-
Third-party Risk
-
Regulatory Risk
-
Theft
-
Employee Threats
How to Mitigate Operational Risk
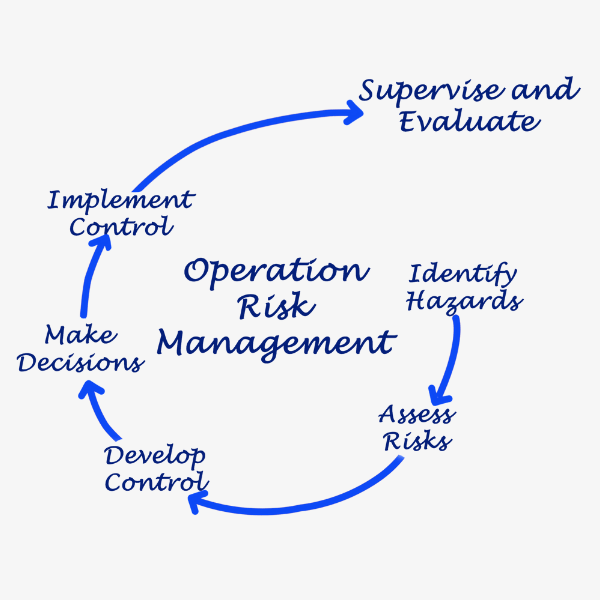 So how can you mitigate operational risk? You complete a detailed risk management plan. As mentioned, operational risks include a vast array of areas. This leaves a difficult, but manageable task for your company. Start by determining responsible parties that will monitor risk and ensure things are palatable. This will typically require performing regular assessments, performing remedial tasks, issuing policies, and monitoring to ensure risk is reducing and compliance is improving.
Your organization could then implement a system for detecting abnormal behavior. Organizations, knowing what to look for, can begin monitoring for suspicious or risky activity. Managers should have a good handle on if their employees are ignoring policies or engaging in tasks outside of their normal job functions. Keep detailed records of everyone’s access and review periodically. Review logs of downloads for sensitive information and scan employee emails for abnormalities.
Restrict access, limit workers to only data necessary for their jobs. Create and enforce policies that require regular maintenance and evaluations. Increase employee training and highlight issues. This all contributes to a safer, more productive, less risky environment.
So how can you mitigate operational risk? You complete a detailed risk management plan. As mentioned, operational risks include a vast array of areas. This leaves a difficult, but manageable task for your company. Start by determining responsible parties that will monitor risk and ensure things are palatable. This will typically require performing regular assessments, performing remedial tasks, issuing policies, and monitoring to ensure risk is reducing and compliance is improving.
Your organization could then implement a system for detecting abnormal behavior. Organizations, knowing what to look for, can begin monitoring for suspicious or risky activity. Managers should have a good handle on if their employees are ignoring policies or engaging in tasks outside of their normal job functions. Keep detailed records of everyone’s access and review periodically. Review logs of downloads for sensitive information and scan employee emails for abnormalities.
Restrict access, limit workers to only data necessary for their jobs. Create and enforce policies that require regular maintenance and evaluations. Increase employee training and highlight issues. This all contributes to a safer, more productive, less risky environment. 
Subscribe for our latest posts
Recent Posts
Categories
Try any of our products, free.
Riskwatch products are easy to use, free to try, and can be customized to fit your business needs.
