Sign up in minutes with your email address.
Take advantage of step-by-step guidance and built-in resources to get your next assessment done.
Up to 3 users, sites, and assessments. What are you waiting for?

Sign up for instant access to a free trial
*Professional email address to activate trial

Monitor data in real time from the dashboard. Easily visualize risk and compliance with your Google Map, Risk Profile and Heat Maps using “drill down” capabilities. Track mitigation progress and closure by using any combination of filters to discover and act on implementation that is lacking in your organization. Measure the standards you have chosen across multiple areas of the enterprise, while filtering information to determine compliance in key areas and overall risk score.
Sign up in minutes with your email address.
Take advantage of step-by-step guidance and built-in resources to get your next assessment done.
Up to 3 users, sites, and assessments. What are you waiting for?
*Professional email address required
Easily estimate the cost of using RiskWatch software.

Onsite Hosting

API & Custom Integrations

Single Sign On

Developer Support

Implementation & Training

Cap Index Basic

Cap Index Premium

Security Gauge Data

WorldAware Data

How many individuals will need to edit data? You are only charged for active users, who can be turned on/off by your designated Admin.
The number of Area’s to assess. An Area is anything that is the target of an assessment, such as a facility, supplier, vendor, asset, client, etc.

The number of content libraries you will need. These are our pre-built standards and regulations. Browse our full selection of libraries here

How many individuals will need to edit data? You are only charged for active users, who can be turned on/off by your designated Admin.
The number of Area’s to assess. An Area is anything that is the target of an assessment, such as a facility, supplier, vendor, asset, client, etc.

The number of content libraries you will need. These are our pre-built standards and regulations. Browse our full selection of libraries here

Onsite Hosting

API & Custom Integrations

Single Sign On

Developer Support

Security Gauge Data

WorldAware Data

Cap Index Basic

Cap Index Premium

Implementation & Training
Extra services/ features not included with every subscription.
Sign a three year contract for an additional 5% off your license fee.
Do you want to sign a 3-year contract for an additional 5% off?
(Annual Subscriptions include a 10% Discount on Licenses.)
The final estimated subscription is:
| Description | Information | Quantity | Price |
|---|---|---|---|
| Discount : | |||
| Total : | /month | ||
No. Our platforms are browser-based and can be used on any device that has a web browser and internet connection.
Get started quickly and easily- we set up and host your software site for you. No servers, no storage, no maintenance.
Additional Licenses, Standards, and Service can be added to Standard and Enterprise Subscriptions.
No. Your software will automatically update to the latest versions for no additional charge.
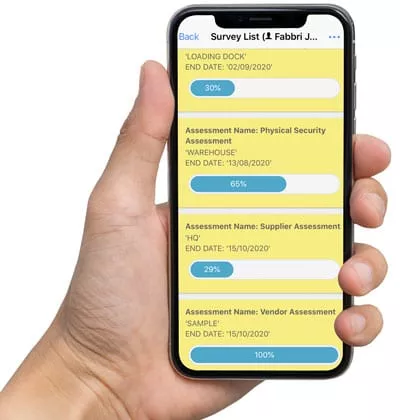
We provide an iOS and Android app that can be used to perform assessments offline.